Definition of Threat Hunting
Threat Hunting is the proactive detection and investigation of malicious activity within a network.
Proactive means a targeted or continuous search for activity even without a evidence for an attack
A sub category of threat hunting is the detection engineering with the following definition:
Detection Engineering is the act of designing and implementing analytics to discover malicious activity.
TTP based Detection
In the opposite of IOC based Detection TTP based detection focuses on more valuable, longer lasting analytics.
To get a feeling for this, have a look to the Pyramid of Pain which looks like this:
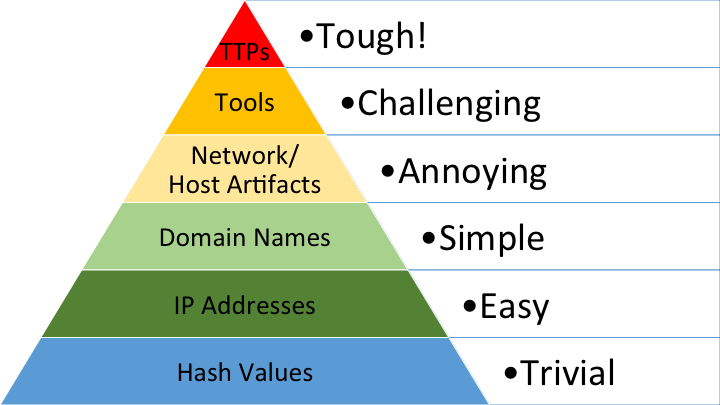
It shows in a very effective way, how much effort an adversary has to spent to change the different types.
As I saw the pyramid for my very first time I thought:
Holy sh!t – yes. It was there in my head all the time. Why didn’t I see that?
Let’s do a comparison between IOC and TTP based detection:
| IOC | TTP |
|---|---|
| Typically, known to be malicious because they have already been used in an intrusion. | Limited by functionality of the underlying technology they target. |
| Therefore they do not help initial victims targeted before the IOC are discovered, shared and implemented by others. | Expensive to develop and maintain an interface. |
| Adversary can easily change them between and within operations. | Therefore, there are limited interfaces provided. |
| Advantage: Adversary | Advantage: Defender |